Kali Linuxが”Penetration Testing Distribution”なのにWindows 10上のWSLで動作するKali LinuxにはPenetration Testingのパッケージが殆ど無いので不思議だったんですよね。
Debian系はまったくの初心者なので調べたらありました。
Kali sources.list Repositories
https://docs.kali.org/general-use/kali-linux-sources-list-repositories
The Kali Rolling Repository
kali-rolling is our current active repository since the release of Kali 2016.1. Kali Rolling users are expected to have the following entries in their sources.list:deb http://http.kali.org/kali kali-rolling main contrib non-free
# For source package access, uncomment the following line
# deb-src http://http.kali.org/kali kali-rolling main contrib non-free
Kali on WSLを確認したらmainだけになっていました。
|
1 2 3 4 5 6 7 8 9 |
rootlinks@Win10:~$ cat /etc/apt/sources.list deb http://http.kali.org/kali kali-rolling main rootlinks@Win10:~$ apt show wpscan Package: wpscan State: not a real package (virtual) N: Can't select candidate version from package wpscan as it has no candidate N: Can't select versions from package 'wpscan' as it is purely virtual N: No packages found |
Repositoriesを追加してupdateします。
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 |
rootlinks@Win10:~$ sudo vi /etc/apt/sources.list [sudo] password for rootlinks: rootlinks@Win10:~$ cat /etc/apt/sources.list #deb http://http.kali.org/kali kali-rolling main deb http://http.kali.org/kali kali-rolling main contrib non-free rootlinks@Win10:~$ sudo apt update Get:1 http://ftp.ne.jp/Linux/packages/kali/kali kali-rolling InRelease [30.5 kB] Get:2 http://ftp.ne.jp/Linux/packages/kali/kali kali-rolling/main amd64 Packages [16.0 MB] Get:3 http://ftp.ne.jp/Linux/packages/kali/kali kali-rolling/contrib amd64 Packages [106 kB] Get:4 http://ftp.ne.jp/Linux/packages/kali/kali kali-rolling/non-free amd64 Packages [164 kB] Fetched 16.3 MB in 57s (285 kB/s) Reading package lists... Done Building dependency tree Reading state information... Done 65 packages can be upgraded. Run 'apt list --upgradable' to see them. W: http: aptMethod::Configuration: could not load seccomp policy: Invalid argument W: http: aptMethod::Configuration: could not load seccomp policy: Invalid argument W: store: aptMethod::Configuration: could not load seccomp policy: Invalid argument |
wpscanのパッケージが見つかりました。
|
1 2 3 4 5 6 7 8 9 10 11 12 13 |
rootlinks@Win10:~$ apt show wpscan Package: wpscan Version: 2.9.3-0kali2 Priority: extra Section: non-free/utils Maintainer: Mati Aharoni <muts@kali.org> Installed-Size: 13.7 MB Depends: ruby | ruby-interpreter, rubygems, bundler, ruby-typhoeus (>= 1.0.0), ruby-nokogiri (>= 1.6.7.2), ruby-terminal-table (>= 1.6.0), ruby-ruby-progressbar (>= 1.6.0~), ruby-addressable, ruby-yajl Homepage: http://www.wpscan.org Download-Size: 1,104 kB APT-Sources: http://http.kali.org/kali kali-rolling/non-free amd64 Packages Description: Black box WordPress vulnerability scanner WPScan scans remote WordPress installations to find security issues. |
wpscanのインストール
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 |
rootlinks@Win10:~$ sudo apt -y install wpscan Reading package lists... Done Building dependency tree Reading state information... Done The following package was automatically installed and is no longer required: libjs-excanvas (snip) rootlinks@Win10:~$ sudo wpscan --help _______________________________________________________________ __ _______ _____ \ \ / / __ \ / ____| \ \ /\ / /| |__) | (___ ___ __ _ _ __ ® \ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \ \ /\ / | | ____) | (__| (_| | | | | \/ \/ |_| |_____/ \___|\__,_|_| |_| WordPress Security Scanner by the WPScan Team Version 2.9.3 Sponsored by Sucuri - https://sucuri.net @_WPScan_, @ethicalhack3r, @erwan_lr, pvdl, @_FireFart_ _______________________________________________________________ Help : Some values are settable in a config file, see the example.conf.json --update Update the database to the latest version. --url | -u <target url> The WordPress URL/domain to scan. --force | -f Forces WPScan to not check if the remote site is running WordPress. --enumerate | -e [option(s)] Enumeration. option : u usernames from id 1 to 10 u[10-20] usernames from id 10 to 20 (you must write [] chars) p plugins vp only vulnerable plugins ap all plugins (can take a long time) tt timthumbs t themes vt only vulnerable themes at all themes (can take a long time) Multiple values are allowed : "-e tt,p" will enumerate timthumbs and plugins If no option is supplied, the default is "vt,tt,u,vp" --exclude-content-based "<regexp or string>" Used with the enumeration option, will exclude all occurrences based on the regexp or string supplied. You do not need to provide the regexp delimiters, but you must write the quotes (simple or double). --config-file | -c <config file> Use the specified config file, see the example.conf.json. --user-agent | -a <User-Agent> Use the specified User-Agent. --cookie <string> String to read cookies from. --random-agent | -r Use a random User-Agent. --follow-redirection If the target url has a redirection, it will be followed without asking if you wanted to do so or not --batch Never ask for user input, use the default behaviour. --no-color Do not use colors in the output. --log [filename] Creates a log.txt file with WPScan's output if no filename is supplied. Otherwise the filename is used for logging. --no-banner Prevents the WPScan banner from being displayed. --disable-accept-header Prevents WPScan sending the Accept HTTP header. --disable-referer Prevents setting the Referer header. --disable-tls-checks Disables SSL/TLS certificate verification. --wp-content-dir <wp content dir> WPScan try to find the content directory (ie wp-content) by scanning the index page, however you can specify it. Subdirectories are allowed. --wp-plugins-dir <wp plugins dir> Same thing than --wp-content-dir but for the plugins directory. If not supplied, WPScan will use wp-content-dir/plugins. Subdirectories are allowed --proxy <[protocol://]host:port> Supply a proxy. HTTP, SOCKS4 SOCKS4A and SOCKS5 are supported. If no protocol is given (format host:port), HTTP will be used. --proxy-auth <username:password> Supply the proxy login credentials. --basic-auth <username:password> Set the HTTP Basic authentication. --wordlist | -w <wordlist> Supply a wordlist for the password brute forcer. --username | -U <username> Only brute force the supplied username. --usernames <path-to-file> Only brute force the usernames from the file. --cache-dir <cache-directory> Set the cache directory. --cache-ttl <cache-ttl> Typhoeus cache TTL. --request-timeout <request-timeout> Request Timeout. --connect-timeout <connect-timeout> Connect Timeout. --threads | -t <number of threads> The number of threads to use when multi-threading requests. --max-threads <max-threads> Maximum Threads. --throttle <milliseconds> Milliseconds to wait before doing another web request. If used, the --threads should be set to 1. --help | -h This help screen. --verbose | -v Verbose output. --version Output the current version and exit. Examples : -Further help ... wpscan --help -Do 'non-intrusive' checks ... wpscan --url www.example.com -Do wordlist password brute force on enumerated users using 50 threads ... wpscan --url www.example.com --wordlist darkc0de.lst --threads 50 -Do wordlist password brute force on the 'admin' username only ... wpscan --url www.example.com --wordlist darkc0de.lst --username admin -Enumerate installed plugins ... wpscan --url www.example.com --enumerate p -Enumerate installed themes ... wpscan --url www.example.com --enumerate t -Enumerate users ... wpscan --url www.example.com --enumerate u -Enumerate installed timthumbs ... wpscan --url www.example.com --enumerate tt -Use a HTTP proxy ... wpscan --url www.example.com --proxy 127.0.0.1:8118 -Use a SOCKS5 proxy ... (cURL >= v7.21.7 needed) wpscan --url www.example.com --proxy socks5://127.0.0.1:9000 -Use custom content directory ... wpscan -u www.example.com --wp-content-dir custom-content -Use custom plugins directory ... wpscan -u www.example.com --wp-plugins-dir wp-content/custom-plugins -Update the DB ... wpscan --update -Debug output ... wpscan --url www.example.com --debug-output 2>debug.log See README for further information. |
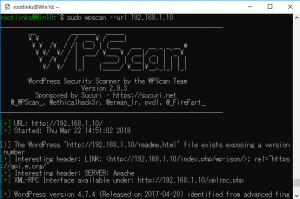
検証環境でscanしてみます。
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 |
rootlinks@Win10:~$ sudo wpscan --url 192.168.1.10 _______________________________________________________________ __ _______ _____ \ \ / / __ \ / ____| \ \ /\ / /| |__) | (___ ___ __ _ _ __ ® \ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \ \ /\ / | | ____) | (__| (_| | | | | \/ \/ |_| |_____/ \___|\__,_|_| |_| WordPress Security Scanner by the WPScan Team Version 2.9.3 Sponsored by Sucuri - https://sucuri.net @_WPScan_, @ethicalhack3r, @erwan_lr, pvdl, @_FireFart_ _______________________________________________________________ [+] URL: http://192.168.1.10/ [+] Started: Thu Mar 22 14:51:02 2018 [!] The WordPress 'http://192.168.1.10/readme.html' file exists exposing a version number [+] Interesting header: LINK: <http://192.168.1.10/index.php/wp-json/>; rel="https://api.w.org/" [+] Interesting header: SERVER: Apache [+] XML-RPC Interface available under: http://192.168.1.10/xmlrpc.php [+] WordPress version 4.7.4 (Released on 2017-04-20) identified from advanced fingerprinting, meta generator, links opml, stylesheets numbers [!] 21 vulnerabilities identified from the version number (snip) |
・readme.htmlからバージョンが知られる
・4.7.4は21の脆弱性が存在する
以降、脆弱性のレファレンスURLや使用しているプラグインと脆弱性が表示されます。
やっとKaliっぽくなってきた。