CentOS 8にtorをインストールしてみました。
CentOS/RHEL/Fedoraにはリポジトリが用意されていますので簡単にインストールできます。
Tor rpm packages
https://support.torproject.org/rpm/
検証環境
・CentOS Linux release 8.2.2004 (Core)
・Kernel 4.18.0-193.6.3.el8_2.x86_64
- epel repositoryの追加
- tor repositoryの追加
- tor install
- /etc/tor/torrcの編集
- 設定ファイルのチェック
- Torの起動
- Firewallの許可
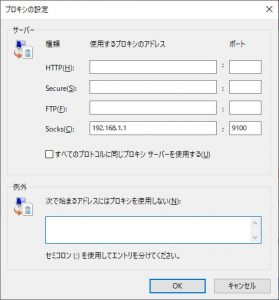
- SOCKS Proxyの設定
- 動作確認
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 |
[root@centos8 ~]# dnf install epel-release -y Last metadata expiration check: 0:09:37 ago on Fri Jun 26 13:05:47 2020. Dependencies resolved. ============================================================================================== Package Architecture Version Repository Size ============================================================================================== Installing: epel-release noarch 8-8.el8 extras 23 k Transaction Summary ============================================================================================== Install 1 Package Total download size: 23 k Installed size: 32 k Downloading Packages: epel-release-8-8.el8.noarch.rpm 331 kB/s | 23 kB 00:00 ---------------------------------------------------------------------------------------------- Total 36 kB/s | 23 kB 00:00 Running transaction check Transaction check succeeded. Running transaction test Transaction test succeeded. Running transaction Preparing : 1/1 Installing : epel-release-8-8.el8.noarch 1/1 Running scriptlet: epel-release-8-8.el8.noarch 1/1 Verifying : epel-release-8-8.el8.noarch 1/1 Installed: epel-release-8-8.el8.noarch Complete! [root@centos8 ~]# dnf info tor Extra Packages for Enterprise Linux Modular 8 - x86_64 125 kB/s | 119 kB 00:00 Extra Packages for Enterprise Linux 8 - x86_64 2.7 MB/s | 7.1 MB 00:02 Available Packages Name : tor Version : 0.4.3.5 Release : 1.el8 Architecture : x86_64 Size : 3.3 M Source : tor-0.4.3.5-1.el8.src.rpm Repository : epel Summary : Anonymizing overlay network for TCP URL : https://www.torproject.org License : BSD Description : The Tor network is a group of volunteer-operated servers that allows people to : improve their privacy and security on the Internet. Tor's users employ this : network by connecting through a series of virtual tunnels rather than making a : direct connection, thus allowing both organizations and individuals to share : information over public networks without compromising their privacy. Along the : same line, Tor is an effective censorship circumvention tool, allowing its : users to reach otherwise blocked destinations or content. Tor can also be used : as a building block for software developers to create new communication tools : with built-in privacy features. : : This package contains the Tor software that can act as either a server on the : Tor network, or as a client to connect to the Tor network. |
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 |
[root@centos8 ~]# vi /etc/yum.repos.d/tor.repo [root@centos8 ~]# cat /etc/yum.repos.d/tor.repo [tor] name=Tor for Enterprise Linux $releasever - $basearch baseurl=https://rpm.torproject.org/centos/$releasever/$basearch enabled=1 gpgcheck=1 gpgkey=https://rpm.torproject.org/centos/public_gpg.key cost=100 [root@centos8 ~]# dnf info tor Tor for Enterprise Linux 8 - x86_64 11 kB/s | 25 kB 00:0 Last metadata expiration check: 0:00:01 ago on Mon Jun 22 11:45:31 2020. Available Packages Name : tor Version : 0.4.3.5 Release : 1.el8 Architecture : src Size : 7.4 M Source : None Repository : tor Summary : Anonymizing overlay network for TCP URL : https://www.torproject.org License : BSD Description : The Tor network is a group of volunteer-operated servers that allows people to : improve their privacy and security on the Internet. Tor's users employ this : network by connecting through a series of virtual tunnels rather than making a : direct connection, thus allowing both organizations and individuals to share : information over public networks without compromising their privacy. Along the : same line, Tor is an effective censorship circumvention tool, allowing its : users to reach otherwise blocked destinations or content. Tor can also be used : as a building block for software developers to create new communication tools : with built-in privacy features. : : This package contains the Tor software that can act as either a server on the : Tor network, or as a client to connect to the Tor network. Name : tor Version : 0.4.3.5 Release : 1.el8 Architecture : x86_64 Size : 3.3 M Source : tor-0.4.3.5-1.el8.src.rpm Repository : epel Summary : Anonymizing overlay network for TCP URL : https://www.torproject.org License : BSD Description : The Tor network is a group of volunteer-operated servers that allows people to : improve their privacy and security on the Internet. Tor's users employ this : network by connecting through a series of virtual tunnels rather than making a : direct connection, thus allowing both organizations and individuals to share : information over public networks without compromising their privacy. Along the : same line, Tor is an effective censorship circumvention tool, allowing its : users to reach otherwise blocked destinations or content. Tor can also be used : as a building block for software developers to create new communication tools : with built-in privacy features. : : This package contains the Tor software that can act as either a server on the : Tor network, or as a client to connect to the Tor network. Name : tor Version : 0.4.3.5 Release : 1.el8 Architecture : x86_64 Size : 3.3 M Source : tor-0.4.3.5-1.el8.src.rpm Repository : tor Summary : Anonymizing overlay network for TCP URL : https://www.torproject.org License : BSD Description : The Tor network is a group of volunteer-operated servers that allows people to : improve their privacy and security on the Internet. Tor's users employ this : network by connecting through a series of virtual tunnels rather than making a : direct connection, thus allowing both organizations and individuals to share : information over public networks without compromising their privacy. Along the : same line, Tor is an effective censorship circumvention tool, allowing its : users to reach otherwise blocked destinations or content. Tor can also be used : as a building block for software developers to create new communication tools : with built-in privacy features. : : This package contains the Tor software that can act as either a server on the : Tor network, or as a client to connect to the Tor network. |
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 |
[root@centos8 ~]# dnf -y install tor Last metadata expiration check: 0:12:24 ago on Fri Jun 26 13:19:27 2020. Dependencies resolved. ============================================================================================== Package Architecture Version Repository Size ============================================================================================== Installing: tor x86_64 0.4.3.5-1.el8 tor 3.3 M Installing dependencies: torsocks x86_64 2.3.0-1.el8 epel 72 k Transaction Summary ============================================================================================== Install 2 Packages Total download size: 3.3 M Installed size: 16 M Downloading Packages: (1/2): torsocks-2.3.0-1.el8.x86_64.rpm 897 kB/s | 72 kB 00:00 (2/2): tor-0.4.3.5-1.el8.x86_64.rpm 1.1 MB/s | 3.3 MB 00:03 ---------------------------------------------------------------------------------------------- Total 914 kB/s | 3.3 MB 00:03 warning: /var/cache/dnf/tor-a35d07c655799cc4/packages/tor-0.4.3.5-1.el8.x86_64.rpm: Header V4 RSA/SHA256 Signature, key ID 3621cd35: NOKEY Tor for Enterprise Linux 8 - x86_64 4.4 kB/s | 3.8 kB 00:00 Importing GPG key 0x3621CD35: Userid : "Kushal Das (RPM Signing key) <kushal@torproject.org>" Fingerprint: 999E C8E3 14BC 8D46 022D 6C7D E217 C30C 3621 CD35 From : https://rpm.torproject.org/centos/public_gpg.key Key imported successfully warning: /var/cache/dnf/epel-6519ee669354a484/packages/torsocks-2.3.0-1.el8.x86_64.rpm: Header V3 RSA/SHA256 Signature, key ID 2f86d6a1: NOKEY Extra Packages for Enterprise Linux 8 - x86_64 1.6 MB/s | 1.6 kB 00:00 Importing GPG key 0x2F86D6A1: Userid : "Fedora EPEL (8) <epel@fedoraproject.org>" Fingerprint: 94E2 79EB 8D8F 25B2 1810 ADF1 21EA 45AB 2F86 D6A1 From : /etc/pki/rpm-gpg/RPM-GPG-KEY-EPEL-8 Key imported successfully Running transaction check Transaction check succeeded. Running transaction test Transaction test succeeded. Running transaction Preparing : 1/1 Installing : torsocks-2.3.0-1.el8.x86_64 1/2 Running scriptlet: tor-0.4.3.5-1.el8.x86_64 2/2 Installing : tor-0.4.3.5-1.el8.x86_64 2/2 Running scriptlet: tor-0.4.3.5-1.el8.x86_64 2/2 Verifying : tor-0.4.3.5-1.el8.x86_64 1/2 Verifying : torsocks-2.3.0-1.el8.x86_64 2/2 Installed: tor-0.4.3.5-1.el8.x86_64 torsocks-2.3.0-1.el8.x86_64 Complete! |
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 192 193 194 195 196 197 198 199 200 201 202 203 204 205 206 207 208 209 210 211 212 213 214 215 216 217 218 219 220 221 222 223 224 225 226 227 228 229 230 231 232 233 234 235 236 237 238 239 240 241 242 243 244 245 246 247 248 249 250 251 252 253 254 255 256 257 258 |
[root@centos8 ~]# cat /etc/tor/torrc ## Configuration file for a typical Tor user ## Last updated 28 February 2019 for Tor 0.3.5.1-alpha. ## (may or may not work for much older or much newer versions of Tor.) ## ## Lines that begin with "## " try to explain what's going on. Lines ## that begin with just "#" are disabled commands: you can enable them ## by removing the "#" symbol. ## ## See 'man tor', or https://www.torproject.org/docs/tor-manual.html, ## for more options you can use in this file. ## ## Tor will look for this file in various places based on your platform: ## https://www.torproject.org/docs/faq#torrc ControlSocket /run/tor/control ControlSocketsGroupWritable 1 CookieAuthentication 1 CookieAuthFile /run/tor/control.authcookie CookieAuthFileGroupReadable 1 ## Tor opens a SOCKS proxy on port 9050 by default -- even if you don't ## configure one below. Set "SOCKSPort 0" if you plan to run Tor only ## as a relay, and not make any local application connections yourself. #SOCKSPort 9050 # Default: Bind to localhost:9050 for local connections. #SOCKSPort 192.168.0.1:9100 # Bind to this address:port too. ## Entry policies to allow/deny SOCKS requests based on IP address. ## First entry that matches wins. If no SOCKSPolicy is set, we accept ## all (and only) requests that reach a SOCKSPort. Untrusted users who ## can access your SOCKSPort may be able to learn about the connections ## you make. #SOCKSPolicy accept 192.168.0.0/16 #SOCKSPolicy accept6 FC00::/7 #SOCKSPolicy reject * ## Logs go to stdout at level "notice" unless redirected by something ## else, like one of the below lines. You can have as many Log lines as ## you want. ## ## We advise using "notice" in most cases, since anything more verbose ## may provide sensitive information to an attacker who obtains the logs. ## ## Send all messages of level 'notice' or higher to /var/log/tor/notices.log #Log notice file /var/log/tor/notices.log ## Send every possible message to /var/log/tor/debug.log #Log debug file /var/log/tor/debug.log ## Use the system log instead of Tor's logfiles #Log notice syslog ## To send all messages to stderr: #Log debug stderr ## Uncomment this to start the process in the background... or use ## --runasdaemon 1 on the command line. This is ignored on Windows; ## see the FAQ entry if you want Tor to run as an NT service. #RunAsDaemon 1 ## The directory for keeping all the keys/etc. By default, we store ## things in $HOME/.tor on Unix, and in Application Data\tor on Windows. #DataDirectory /var/lib/tor ## The port on which Tor will listen for local connections from Tor ## controller applications, as documented in control-spec.txt. #ControlPort 9051 ## If you enable the controlport, be sure to enable one of these ## authentication methods, to prevent attackers from accessing it. #HashedControlPassword 16:872860B76453A77D60CA2BB8C1A7042072093276A3D701AD684053EC4C #CookieAuthentication 1 ############### This section is just for location-hidden services ### ## Once you have configured a hidden service, you can look at the ## contents of the file ".../hidden_service/hostname" for the address ## to tell people. ## ## HiddenServicePort x y:z says to redirect requests on port x to the ## address y:z. #HiddenServiceDir /var/lib/tor/hidden_service/ #HiddenServicePort 80 127.0.0.1:80 #HiddenServiceDir /var/lib/tor/other_hidden_service/ #HiddenServicePort 80 127.0.0.1:80 #HiddenServicePort 22 127.0.0.1:22 ################ This section is just for relays ##################### # ## See https://www.torproject.org/docs/tor-doc-relay for details. ## Required: what port to advertise for incoming Tor connections. #ORPort 9001 ## If you want to listen on a port other than the one advertised in ## ORPort (e.g. to advertise 443 but bind to 9090), you can do it as ## follows. You'll need to do ipchains or other port forwarding ## yourself to make this work. #ORPort 443 NoListen #ORPort 127.0.0.1:9090 NoAdvertise ## If you want to listen on IPv6 your numeric address must be explictly ## between square brackets as follows. You must also listen on IPv4. #ORPort [2001:DB8::1]:9050 ## The IP address or full DNS name for incoming connections to your ## relay. Leave commented out and Tor will guess. #Address noname.example.com ## If you have multiple network interfaces, you can specify one for ## outgoing traffic to use. ## OutboundBindAddressExit will be used for all exit traffic, while ## OutboundBindAddressOR will be used for all OR and Dir connections ## (DNS connections ignore OutboundBindAddress). ## If you do not wish to differentiate, use OutboundBindAddress to ## specify the same address for both in a single line. #OutboundBindAddressExit 10.0.0.4 #OutboundBindAddressOR 10.0.0.5 ## A handle for your relay, so people don't have to refer to it by key. ## Nicknames must be between 1 and 19 characters inclusive, and must ## contain only the characters [a-zA-Z0-9]. ## If not set, "Unnamed" will be used. #Nickname ididnteditheconfig ## Define these to limit how much relayed traffic you will allow. Your ## own traffic is still unthrottled. Note that RelayBandwidthRate must ## be at least 75 kilobytes per second. ## Note that units for these config options are bytes (per second), not ## bits (per second), and that prefixes are binary prefixes, i.e. 2^10, ## 2^20, etc. #RelayBandwidthRate 100 KBytes # Throttle traffic to 100KB/s (800Kbps) #RelayBandwidthBurst 200 KBytes # But allow bursts up to 200KB (1600Kb) ## Use these to restrict the maximum traffic per day, week, or month. ## Note that this threshold applies separately to sent and received bytes, ## not to their sum: setting "40 GB" may allow up to 80 GB total before ## hibernating. ## ## Set a maximum of 40 gigabytes each way per period. #AccountingMax 40 GBytes ## Each period starts daily at midnight (AccountingMax is per day) #AccountingStart day 00:00 ## Each period starts on the 3rd of the month at 15:00 (AccountingMax ## is per month) #AccountingStart month 3 15:00 ## Administrative contact information for this relay or bridge. This line ## can be used to contact you if your relay or bridge is misconfigured or ## something else goes wrong. Note that we archive and publish all ## descriptors containing these lines and that Google indexes them, so ## spammers might also collect them. You may want to obscure the fact that ## it's an email address and/or generate a new address for this purpose. ## ## If you are running multiple relays, you MUST set this option. ## #ContactInfo Random Person <nobody AT example dot com> ## You might also include your PGP or GPG fingerprint if you have one: #ContactInfo 0xFFFFFFFF Random Person <nobody AT example dot com> ## Uncomment this to mirror directory information for others. Please do ## if you have enough bandwidth. #DirPort 9030 # what port to advertise for directory connections ## If you want to listen on a port other than the one advertised in ## DirPort (e.g. to advertise 80 but bind to 9091), you can do it as ## follows. below too. You'll need to do ipchains or other port ## forwarding yourself to make this work. #DirPort 80 NoListen #DirPort 127.0.0.1:9091 NoAdvertise ## Uncomment to return an arbitrary blob of html on your DirPort. Now you ## can explain what Tor is if anybody wonders why your IP address is ## contacting them. See contrib/tor-exit-notice.html in Tor's source ## distribution for a sample. #DirPortFrontPage /etc/tor/tor-exit-notice.html ## Uncomment this if you run more than one Tor relay, and add the identity ## key fingerprint of each Tor relay you control, even if they're on ## different networks. You declare it here so Tor clients can avoid ## using more than one of your relays in a single circuit. See ## https://www.torproject.org/docs/faq#MultipleRelays ## However, you should never include a bridge's fingerprint here, as it would ## break its concealability and potentially reveal its IP/TCP address. ## ## If you are running multiple relays, you MUST set this option. ## ## Note: do not use MyFamily on bridge relays. #MyFamily $keyid,$keyid,... ## Uncomment this if you want your relay to be an exit, with the default ## exit policy (or whatever exit policy you set below). ## (If ReducedExitPolicy, ExitPolicy, or IPv6Exit are set, relays are exits. ## If none of these options are set, relays are non-exits.) #ExitRelay 1 ## Uncomment this if you want your relay to allow IPv6 exit traffic. ## (Relays do not allow any exit traffic by default.) #IPv6Exit 1 ## Uncomment this if you want your relay to be an exit, with a reduced set ## of exit ports. #ReducedExitPolicy 1 ## Uncomment these lines if you want your relay to be an exit, with the ## specified set of exit IPs and ports. ## ## A comma-separated list of exit policies. They're considered first ## to last, and the first match wins. ## ## If you want to allow the same ports on IPv4 and IPv6, write your rules ## using accept/reject *. If you want to allow different ports on IPv4 and ## IPv6, write your IPv6 rules using accept6/reject6 *6, and your IPv4 rules ## using accept/reject *4. ## ## If you want to _replace_ the default exit policy, end this with either a ## reject *:* or an accept *:*. Otherwise, you're _augmenting_ (prepending to) ## the default exit policy. Leave commented to just use the default, which is ## described in the man page or at ## https://www.torproject.org/documentation.html ## ## Look at https://www.torproject.org/faq-abuse.html#TypicalAbuses ## for issues you might encounter if you use the default exit policy. ## ## If certain IPs and ports are blocked externally, e.g. by your firewall, ## you should update your exit policy to reflect this -- otherwise Tor ## users will be told that those destinations are down. ## ## For security, by default Tor rejects connections to private (local) ## networks, including to the configured primary public IPv4 and IPv6 addresses, ## and any public IPv4 and IPv6 addresses on any interface on the relay. ## See the man page entry for ExitPolicyRejectPrivate if you want to allow ## "exit enclaving". ## #ExitPolicy accept *:6660-6667,reject *:* # allow irc ports on IPv4 and IPv6 but no more #ExitPolicy accept *:119 # accept nntp ports on IPv4 and IPv6 as well as default exit policy #ExitPolicy accept *4:119 # accept nntp ports on IPv4 only as well as default exit policy #ExitPolicy accept6 *6:119 # accept nntp ports on IPv6 only as well as default exit policy #ExitPolicy reject *:* # no exits allowed ## Bridge relays (or "bridges") are Tor relays that aren't listed in the ## main directory. Since there is no complete public list of them, even an ## ISP that filters connections to all the known Tor relays probably ## won't be able to block all the bridges. Also, websites won't treat you ## differently because they won't know you're running Tor. If you can ## be a real relay, please do; but if not, be a bridge! ## ## Warning: when running your Tor as a bridge, make sure than MyFamily is ## NOT configured. #BridgeRelay 1 ## By default, Tor will advertise your bridge to users through various ## mechanisms like https://bridges.torproject.org/. If you want to run ## a private bridge, for example because you'll give out your bridge ## address manually to your friends, uncomment this line: #PublishServerDescriptor 0 ## Configuration options can be imported from files or folders using the %include ## option with the value being a path. If the path is a file, the options from the ## file will be parsed as if they were written where the %include option is. If ## the path is a folder, all files on that folder will be parsed following lexical ## order. Files starting with a dot are ignored. Files on subfolders are ignored. ## The %include option can be used recursively. #%include /etc/torrc.d/ #%include /etc/torrc.custom |
検証に必要な最低限の設定です。
|
1 2 3 4 5 6 7 8 9 |
# インターフェース:ポート SOCKSPort 9050 # Default: Bind to localhost:9050 for local connections. SOCKSPort 192.168.1.1:9100 # Bind to this address:port too. # 許可するネットワーク SOCKSPolicy accept 127.0.0.1 SOCKSPolicy accept 192.168.1.0/24 SOCKSPolicy reject * # ログ Log notice file /var/log/tor/notices.log |
rootでtorを実行していると警告でていますが、取り合えず検証なので無視します(^^;
|
1 2 3 4 5 6 |
[root@centos8 ~]# tor -f /etc/tor/torrc --verify-config Jun 20 13:43:10.849 [notice] Tor 0.4.3.5 running on Linux with Libevent 2.1.8-stable, OpenSSL 1.1.1c, Zlib 1.2.11, Liblzma 5.2.4, and Libzstd 1.4.2. Jun 20 13:43:10.849 [notice] Tor can't help you if you use it wrong! Learn how to be safe at https://www.torproject.org/download/download#warning Jun 20 13:43:10.849 [notice] Read configuration file "/etc/tor/torrc". Jun 20 13:43:10.851 [warn] You are running Tor as root. You don't need to, and you probably shouldn't. Configuration was valid |
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 |
[root@centos8 ~]# systemctl start tor [root@centos8 ~]# systemctl status tor * tor.service - Anonymizing overlay network for TCP Loaded: loaded (/usr/lib/systemd/system/tor.service; enabled; vendor preset: disabled) Active: active (running) since Fri 2020-06-20 13:47:55 JST; 7s ago Process: 6019 ExecStartPre=/usr/bin/tor --runasdaemon 0 --defaults-torrc /usr/share/tor/def> Main PID: 6021 (tor) Tasks: 1 (limit: 49603) Memory: 21.2M CGroup: /system.slice/tor.service `-6021 /usr/bin/tor --runasdaemon 0 --defaults-torrc /usr/share/tor/defaults-torrc> Jun 20 13:47:55 centos8.rootlinks.net tor[6019]: Jun 20 13:47:55.304 [notice] Read configurat> Jun 20 13:47:55 centos8.rootlinks.net tor[6019]: Configuration was valid Jun 20 13:47:55 centos8.rootlinks.net tor[6021]: Jun 20 13:47:55.340 [notice] Tor 0.4.3.5 run> Jun 20 13:47:55 centos8.rootlinks.net tor[6021]: Jun 20 13:47:55.340 [notice] Tor can't help > Jun 20 13:47:55 centos8.rootlinks.net tor[6021]: Jun 20 13:47:55.340 [notice] Read configurat> Jun 20 13:47:55 centos8.rootlinks.net tor[6021]: Jun 20 13:47:55.340 [notice] Read configurat> Jun 20 13:47:55 centos8.rootlinks.net tor[6021]: Jun 20 13:47:55.342 [notice] You configured > Jun 20 13:47:55 centos8.rootlinks.net tor[6021]: Jun 20 13:47:55.342 [notice] Opening Socks l> Jun 20 13:47:55 centos8.rootlinks.net tor[6021]: Jun 20 13:47:55.342 [notice] Opened Socks li> Jun 20 13:47:55 centos8.rootlinks.net systemd[1]: Started Anonymizing overlay network for TCP. |
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 |
[root@centos8 ~]# firewall-cmd --permanent --add-rich-rule="rule family="ipv4" source address="192.168.1.0/24" port protocol="tcp" port="9100" accept" success [root@centos8 ~]# firewall-cmd --reload success [root@centos8 ~]# firewall-cmd --list-all public (active) target: default icmp-block-inversion: no interfaces: ens160 sources: services: cockpit dhcpv6-client ssh ports: protocols: masquerade: no forward-ports: source-ports: icmp-blocks: rich rules: rule family="ipv4" source address="192.168.1.0/24" port port="9100" protocol="tcp" accept |
https://check.torproject.org/ にアクセスして下記の画面が表示されればTor経由になっています。